可怕!ヽ(*。>Д<)o゜
事先声明:团队有且只有 [email protected] 和 [email protected] 这两个官方邮箱地址
不要轻信“垃圾邮件”文件夹中的所有邮件,如有必要请与官方团队核实!
摘要
坛主于 2026-02-18 01:18(UTC) 收到了一封可疑的网络钓鱼邮件,发信人为 <[email protected]>,收件人为 [email protected]。根据团队内部核实,确认团队不存在 [email protected] 邮箱地址,该邮件显示出典型的伪造和钓鱼迹象。其意图似乎是通过伪装成邮箱存储管理门户,通过欺骗性链接来窃取凭证。主要发现包括使用混淆内容、可疑域名重定向,以及与高滥用顶级域名(TLDs)。目标链接相关的 .sbs TLD 在最近调查中报告的滥用率高达 225.9。
值得一提的是,团队在当日 13:48(UTC) 又收到了相同内容的钓鱼邮件。两封邮件的正文均不包含跟踪器。
两封钓鱼邮件均未通过 DKIM 签名验证,均进入“垃圾邮件”文件夹。
邮件头部分析
邮件通过多个中继传输,从 Google Cloud IP(35.204..)开始,经过团队邮箱服务器抵达。经过团队安全部门分析,邮件原文中的发件人部分为空(<>),由此可见这并非常规邮件,团队内部的垃圾邮件过滤器成功识别并过滤。邮件头部标有高优先级标志(Importance: high, X-Priority: 1)。
内容上使用 base64 编码纯文本和 HTML 部分,这是一种用于规避垃圾邮件检测的技术。MIME-Version: 1.0 和 multipart/alternative 结构模仿专业邮件。
发件人分析
通过 Google Cloud 的虚拟实例发送,常见于钓鱼邮件。
内容分析
主题:“[[email protected]]: Please confirm to continue.”
伪装成内部支持以建立信任。
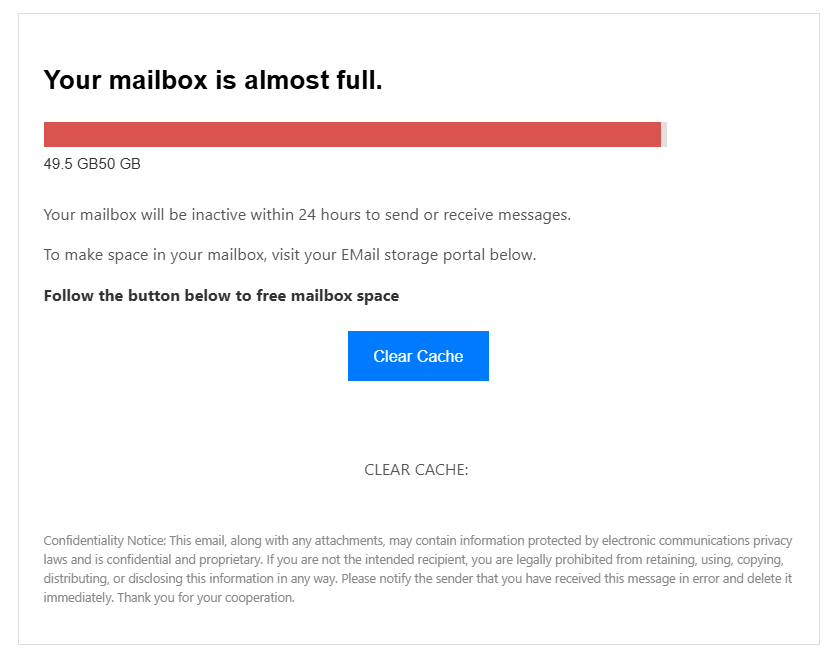
正文:声称邮箱几乎已满(49.5 GB / 50 GB),并将在24小时内无法发送/接收邮件,敦促采取行动。这种基于恐惧的策略是钓鱼的标志,迫使团队成员在未验证的情况下点击。
正文还包括 HTML 元素,为进度条(红色背景,以制造紧迫感)和“Clear Cache”按钮,结尾处还有保密声明,用于模仿企业邮件。
值得一提的是,正文内容的“EMail storage portal”大小写编写不当。
链接和重定向分析
嵌入链接的结构为 https://juguetes[删除防止有人上当].com.ar/Banner.php?id=21&url=https://do[删除防止有人上当].sbs/tang/index.html?email=[Email]。
其中 juguetes[删除防止有人上当].com.ar 为一个合法的阿根廷玩具公司网站,成立于 1990 年代。/Banner.php 路径表明可能被入侵,例如注入重定向脚本。
其目标为 do[删除防止有人上当].sbs。.sbs TLD 被标记为高钓鱼滥用,在最近几个月中有 10% 的域名被列为恶意。Spamhaus 报告 .sbs 增长率为 172%,滥用率升高,因为注册成本低,常被用于凭证窃取。在 Reddit 等平台上的用户报告了来自 .sbs 域名的垃圾邮件,浏览显示“Insufficient relevant content”或 Cloudflare 验证,这常见于隐藏钓鱼页面,用于动态加载以规避检测。
目的可能为窃取凭证(如电子邮件/密码),?email=[Email] 参数表明其很可能为预填充表单。
结语
可怕捏!ヽ(*。>Д<)o゜